Litecoin Rewinds 13 Blocks After Exploit, Patch Timeline Raises Questions
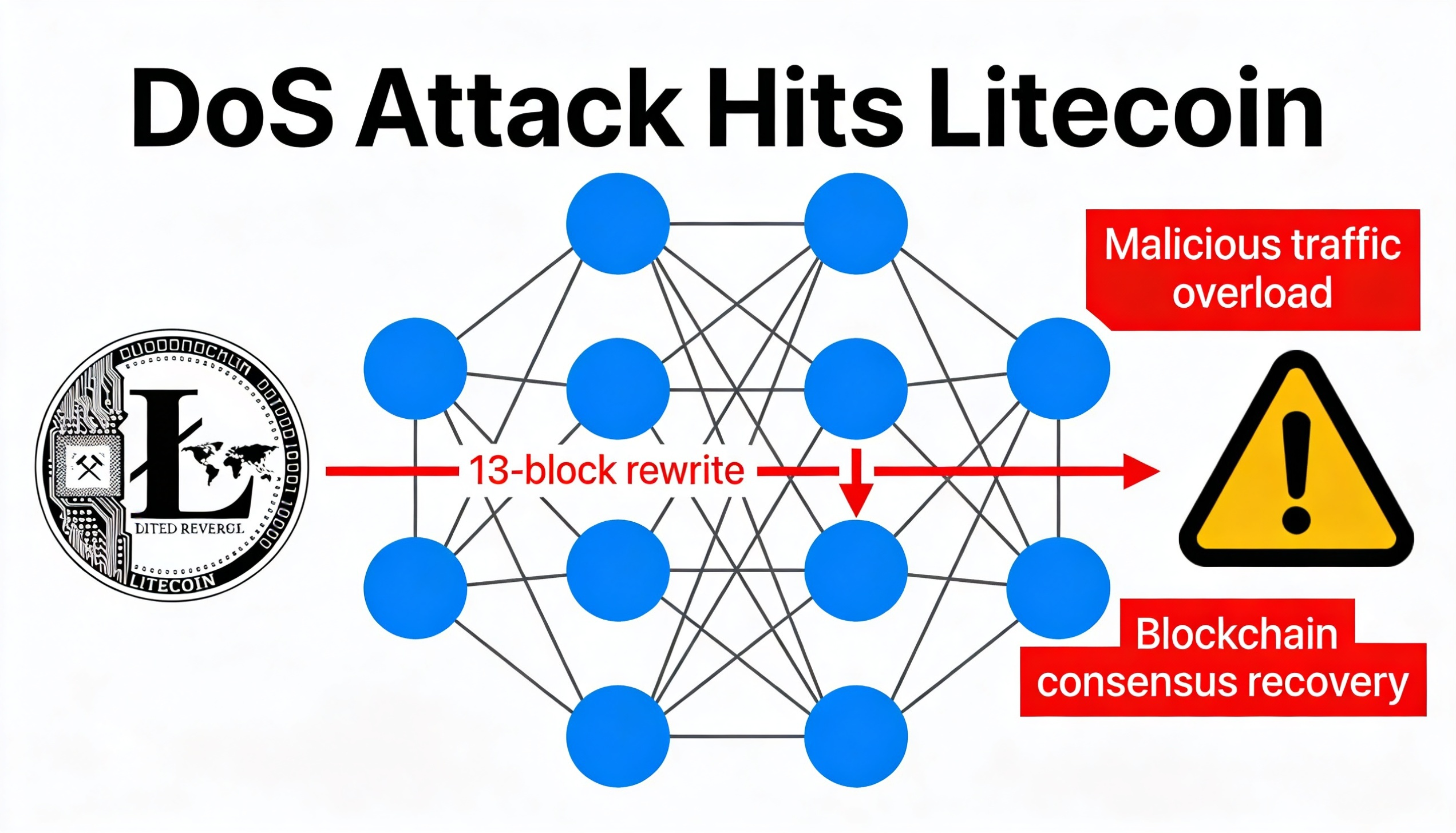
Litecoin underwent a 13-block chain reorganization late Friday into Saturday, rolling back roughly 32 minutes of activity after attackers exploited a vulnerability in its Mimblewimble Extension Block (MWEB) protocol.
The flaw allowed invalid MWEB transactions to pass through nodes that had not yet been updated, enabling a denial-of-service (DoS) attack that disrupted major mining pools. The issue was ultimately resolved as the network reverted to the longest valid chain, effectively undoing the malicious activity.
The Litecoin Foundation described the incident as a zero-day exploit and said Sunday morning in Asia that the vulnerability had been fully patched, with the network now operating normally.
However, independent researchers have raised concerns about that characterization. According to analysis of the litecoin-project GitHub repository, the underlying consensus vulnerability had been identified and privately patched weeks before the attack.
Security researcher “bbsz,” affiliated with the SEAL911 crypto incident response group, highlighted the timeline using public commit data. The consensus flaw enabling invalid MWEB peg-out transactions was quietly fixed between March 19 and March 26 — more than four weeks prior to the exploit.
A separate denial-of-service vulnerability was addressed on April 25, shortly before both fixes were bundled into release version 0.21.5.4 later that same day, after the attack had already begun.
The repository history suggests that while the vulnerability had been resolved in code, the patch was not widely disclosed or enforced across the network, leaving some mining pools and nodes exposed.
The episode underscores ongoing challenges in coordinating timely updates across decentralized networks, particularly when critical fixes are not immediately adopted by all participants.